Cyber Warfare, explained
Geopolitics, Zero-days and Incidents
May 12, 2026
Cyber warfare is the use of digital tools by states to spy on, damage or pressure other states.
Some countries use cyber tools to steal money as a source of income.
Digital (or cyber) space is now seen as the 5th area of military activity, alongside land, sea, air and space.
Cyber space has no international treaty. There is no agreement on what counts as an act of war, and what is a legal response to a state-sponsored cyberattack.
A zero-day is a flaw in a computer program that is known to hackers but not to the developer.
A zero-day can be hidden until used to attack a system.
Other cyberweapons include:
Malware: “virus” software made to damage computers or steal data.
Ransomware: malware that locks files until a payment is made.
Phishing: fake messages pretending to be legitimate websites or services to trick people into giving away passwords or installing malware.
DDoS: overloading a computer system with a very large number of fake requests (“Distributed Denial-of-Service”).
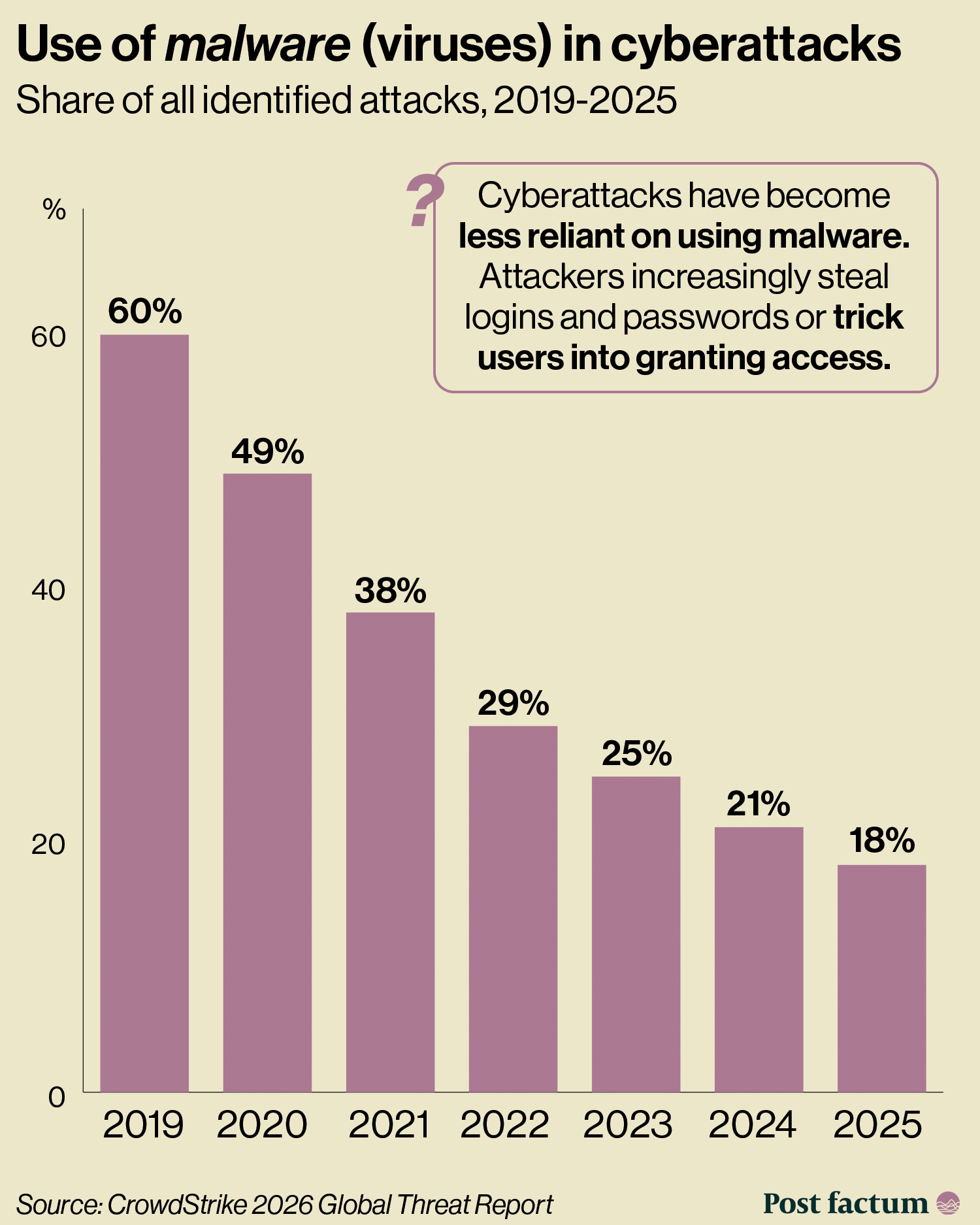
In recent years, cyberattacks are more often focused on tricking the humans involved in the computer systems.
The use of malware in cyberattacks fell from 60% in 2019 to 18% in 2025.
Social engineering is the manipulation of human psychology to get secret or private information.
For example, pretending to be someone else to log into their account through a customer support service.
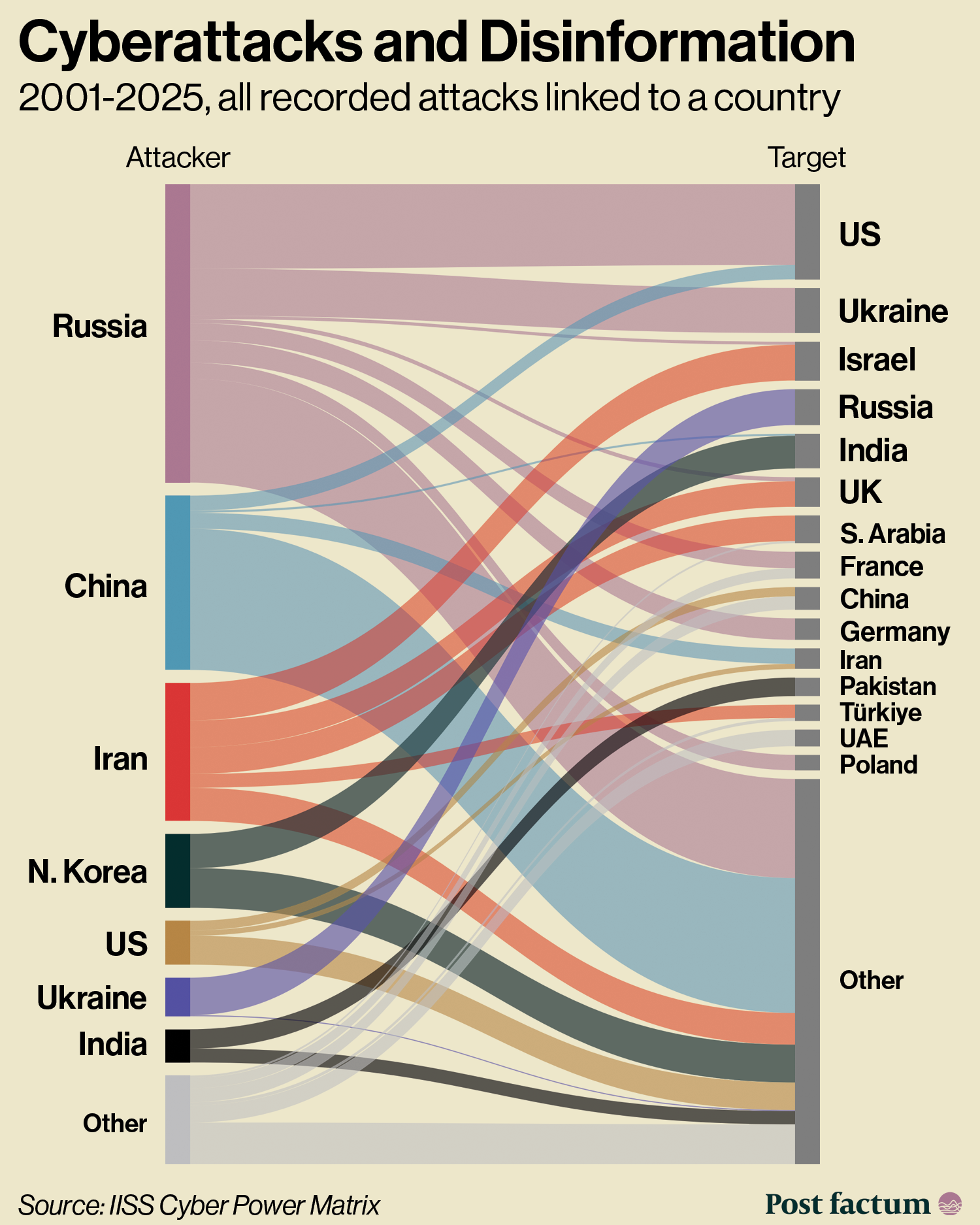
In 2000-2023, China was behind 22% of known cyber attacks, followed by Russia (21%), Iran (10%), North Korea (9%), Ukraine (5%) and the US (4%).
Russia takes the first place if both cyberattacks and disinformation campaigns are counted together.
China, Russia, Iran and North Korea share malware and intelligence in informal cyber cooperation, with Russia and Iran signing a cyber agreement in 2021.
In 2025, attacks involving AI rose 89% year-on-year.
AI can be used to generate malware code, create fake content for disinformation campaigns, and more.
A pro-Russia hacking group put an AI language model directly into its malware to generate commands on the go, the first known case of AI running inside an attack tool.
In 2026, AI has become a major part of cybersecurity, as the latest models can be better than humans at finding bugs and even zero-days.
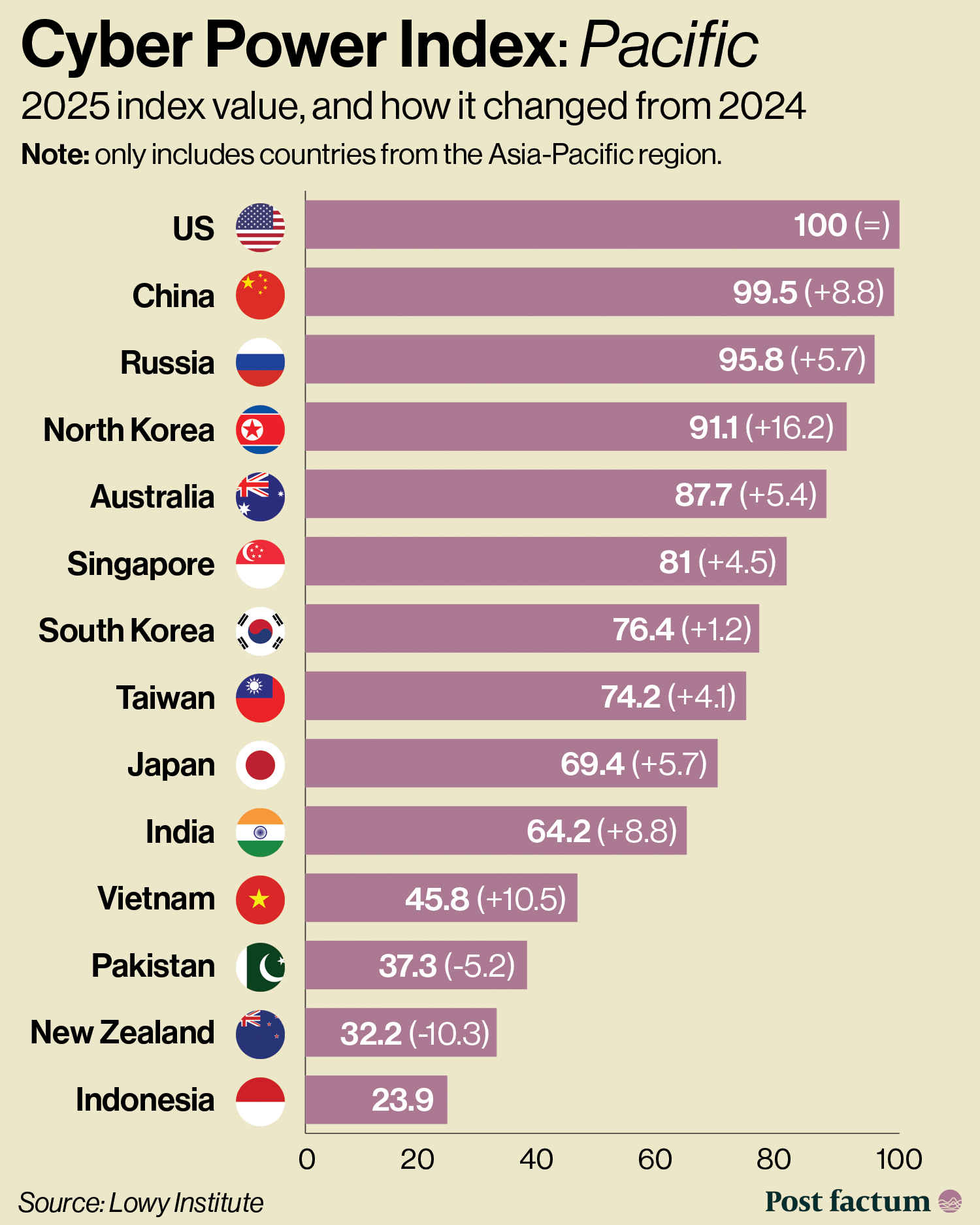
China
China treats peacetime as continuous cyber competition, focused on data and trade-secret theft.
Chinese groups have stolen personal data on about 80% of Americans since 2014.
In 2025, China-linked attacks grew 38% globally, with attacks on logistics up by 85%.
In 2023 and 2024, the US found that Chinese hackers have had quiet access to some important systems like water facilities and telecommunications, including the infrastructure for recording phone calls.
In 2024, China created a separate Cyberspace Force within its military.
Russia
Russia avoids the word cyber in its military doctrines, calling it “informational competition”.
In 2022, Russian military hackers damaged tens of thousands of internet receivers (modems) in Ukraine and elsewhere in Europe just before the invasion.
In 2008, Russian hackers used DDoS attacks against the Georgian government’s website and services before an invasion.
Iran
Iran's cyber operations are run by the Revolutionary Guards and the intelligence ministry.
Iran is less advanced than Russia or China but more willing to damage civilian targets, including a 2023 attack on US water utilities.
After the June 2025 bombing campaign by Israel and the US, Iranian attacks on Israeli targets rose by 700%.
Iran is building a national intranet (closed internet with controlled content), to have the ability to cut the population off from the global internet during protests.
US
The US has a strong capability for offensive cyberattacks but weaker and unorganised defence.
US Cyber Command has 133 teams of 6,000 people total, spread between offensive (40), defensive (68) and support (25).
The 2023 Cybersecurity Strategy was replaced in March 2026 by a brief (7 pages) "Cyber Strategy for America" that drops new regulations in favour of offensive disruption.
Some critical infrastructure in the US is operated by private companies, making it harder for the government to control the strength of cyber defence there.
The US company Anthropic released its latest model to selected US technology and services companies to improve their cyber defences.
North Korea
North Korea uses cyber mostly as a revenue source, especially by stealing crypto.
Its hacker group stole $1.5 billion in crypto from a Dubai exchange in February 2025, the largest single financial theft on record.
In addition, North Korea earned $0.8 billion in 2024 alone through people working remotely for Western companies under fake identities.
Around 60% of all crypto stolen worldwide in 2024-25 went to North Korean hackers.
History of Cyber in 8 Attacks
Stuxnet (2010): a US-Israeli operation destroyed about 1,000 centrifuges at Iran's nuclear plant.
The malware reached the plant on a USB stick and re-programmed the centrifuges to spin themselves to destruction while reporting normal readings.
This was the first cyberweapon to cause physical damage.
Sony Pictures hack (2014): a North Korean group attacked the US film studio in revenge for a comedy movie mocking the North Korean regime.
Hackers leaked 5 unreleased films, as well as private data and internal emails from 47,000 employees.
This was the first destructive attack the US attributed to a specific state.
Ukrainian power grid (2015): Russian military hackers cut power to about 225,000 customers in western Ukraine for 6 hours.
Hackers also erased all data from the computers used and overloaded support centres with fake phone calls.
The first publicly confirmed power blackout from a cyberattack.
US Democrats hack (2016): Russian hackers broke into the emails of the Democratic National Committee and Hillary Clinton's campaign chairman, leaking data.
Stolen files were published through websites like WikiLeaks.
First known cyberattack aimed directly at the US presidential election.
WannaCry (2017): a North Korean ransomware infected over 200,000 machines across 150 countries, with the UK's NHS cancelling around 19,000 appointments.
It was built using tools stolen from a US federal cyber service (NSA) by hackers with unknown motives, the Shadow Brokers.
First globally self-spreading ransomware “worm”.
NotPetya (2017): a Russian cyberweapon designed to destroy computers. It was used against Ukraine but spread globally causing over $10 billion in damage.
NotPetya was made to look like ransomware but there was no way to unblock the data which was destroyed. It was deployed into Ukrainian tax software but escaped through corporate networks and damaged companies like FedEx and Maersk.
The costliest attack in history so far, the first destructive virus of global scale.
SolarWinds (2020): Russia's foreign intelligence inserted a hidden backdoor into signed updates of a network management tool used by about 18,000 organisations globally.
Russia used this to get hidden access to 9 US federal departments, including the Treasury, for 9 months, until discovered by a private security firm.
This was a supply-chain compromise, meaning attacking a target by getting access to some software it would then buy or use.
Colonial Pipeline (2021): a ransomware attack shut down the largest US fuel pipeline for 6 days causing panic buying and security concerns.
The hackers got access through a single old password without 2-factor protection. The company paid $4.4 million in Bitcoin as ransom; the FBI then recovered $2.3 million of that.
This attack led to the US passing a number of laws regulating cyber incidents connected to critical infrastructure.
Thank you for reading!
Author Anton Kutuzov
Join Post factum Pro to see the comment section below.
